Snowflake Azure PrivateLink Implementation Runbook
Last updated: November 2024
Quick answer: To set up Azure PrivateLink for Snowflake, create a Resource Group, VNet, and subnet in Azure, then deploy a Private Endpoint targeting Snowflake's PrivateLink resource ID. Configure a Private DNS Zone for privatelink.snowflakecomputing.com, run SYSTEM$AUTHORIZE_PRIVATELINK in Snowflake to approve the endpoint, and validate connectivity using nslookup and SnowSQL over the private connection.
Business Critical Edition | Azure (East US 2) | End-to-end: Azure + Snowflake + DNS + Validation
1. Purpose and Scope
This Snowflake Azure PrivateLink implementation runbook provides a complete, step-by-step procedure to enable PrivateLink on Microsoft Azure for a Snowflake Business Critical account. It covers all required Azure networking steps (Resource Group, VNet, Subnets, Private Endpoint, Private DNS Zone), Snowflake authorization commands, DNS validation tests, common pitfalls, and secure access methods via Bastion or VPN. For data loading over this private connection, see our guide to loading data from Azure Cloud to Snowflake.
1.1 Target account details
| Field | Value |
|---|---|
| Account URL (public) | TVYPIHZ-YCA28219.snowflakecomputing.com |
| Account Locator | DLA03063 |
| Cloud | Azure |
| Region | East US 2 |
| Edition | Business Critical |
Authoritative Snowflake PrivateLink configuration (output of SYSTEM$GET_PRIVATELINK_CONFIG()):
{
"privatelink-account-name": "dla03063.east-us-2.privatelink",
"privatelink-pls-id": "sf-pvlinksvc-azeastus2prodshard2.ffc74fdb-c717-4c57-a041-8a8c52243329.eastus2.azure.privatelinkservice",
"snowpark-connect-privatelink-url": "*.snowpark.iadzpr.privatelink.snowflakecomputing.com",
"openflow-privatelink-url": "tvypihz-yca28219.openflow.iadzpr.privatelink.snowflakecomputing.com",
"app-service-privatelink-url": "*.iadzpr.privatelink.snowflake.app",
"regionless-snowsight-privatelink-url": "app-tvypihz-yca28219.privatelink.snowflakecomputing.com",
"external-telemetry-privatelink-url": "tvypihz-yca28219.telemetry.iadzpr.privatelink.snowflakecomputing.com",
"snowsight-privatelink-url": "app.east-us-2.privatelink.snowflakecomputing.com",
"regionless-privatelink-ocsp-url": "ocsp.tvypihz-yca28219.privatelink.snowflakecomputing.com",
"privatelink-account-url": "dla03063.east-us-2.privatelink.snowflakecomputing.com",
"spcs-registry-privatelink-url": "tvypihz-yca28219.registry.privatelink.snowflakecomputing.com",
"regionless-privatelink-account-url": "tvypihz-yca28219.privatelink.snowflakecomputing.com",
"spcs-auth-privatelink-url": "sfc-endpoint-login.iadzpr.privatelink.snowflakecomputing.com",
"privatelink_ocsp-url": "ocsp.dla03063.east-us-2.privatelink.snowflakecomputing.com"
}
1.2 High-level architecture
PrivateLink traffic flow:
- Client workload (VMs, apps) runs inside an Azure Virtual Network (VNet).
- Azure Private Endpoint provides a private IP in the VNet that connects to Snowflake’s Azure Private Link Service (PLS).
- Azure Private DNS resolves Snowflake PrivateLink hostnames (SQL, Snowsight, OCSP, etc.) to the Private Endpoint IP.
- After validation, Snowflake can optionally be locked down to PrivateLink-only inbound access.
-
Client / VM / App
|
| (Private DNS)
v
|
v
Azure Private Endpoint (NIC: 10.x.x.x)
|
v
Snowflake Service (Azure)
2. Prerequisites
2.1 Access and Roles
- Snowflake: ACCOUNTADMIN role required for SYSTEM$* PrivateLink functions (SYSTEM$GET_PRIVATELINK_CONFIG, SYSTEM$AUTHORIZE_PRIVATELINK, SYSTEM$ENFORCE_PRIVATELINK, etc.).
- Azure: Permissions to create Resource Groups, VNets, Subnets, Private Endpoints, Private DNS Zones, and to link DNS zones to VNets.
3. Azure Implementation Steps (Create if needed)
3.1 Create Resource Group
- 1. Azure Portal -> Resource groups -> Create.
- 2. Select the subscription and region (use East US 2 for consistency).
- 3. Name suggestion: rg-snowflake-privatelink-prod.
- 4. Review + Create -> Create.
3.2 Create Virtual Network (VNet)
- 5. Azure Portal -> Virtual networks -> Create.
- 6. Basics: select the resource group and region (East US 2).
- 7. IP Addresses: define an address space (example: 10.0.0.0/16).
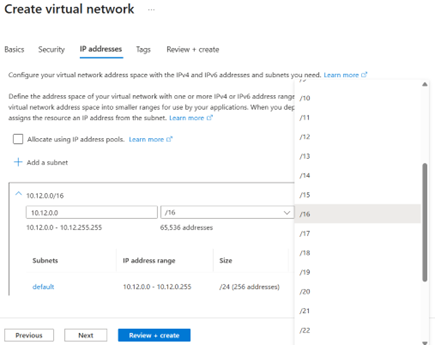
- 8. Create subnets as described below or proceed to create and add subnets after VNet creation.
- 9. Review + Create -> Create.
3.3 Create Required Subnets
3.3.1 Create Private Endpoint Subnet
The Private Endpoint subnet must have network policies disabled. This is a requirement for Azure Private Endpoints to function correctly.
- 10. Open the VNet -> Subnets -> Add subnet.
- 11. Name: snet-privatelink-snowflake (example).
- 12. Subnet range (example): 10.0.0.0/24.
- 13. Disable private endpoint network policies (required for Private Endpoint).
- 14. Save.
3.4 Create Azure Private Endpoint
Before creating the Private Endpoint, run SYSTEM$GET_PRIVATELINK_CONFIG() in Snowflake (as ACCOUNTADMIN) and copy the privatelink-pls-id value. This PLS ID identifies Snowflake's Azure Private Link Service that your endpoint will connect to.
- 15. Azure Portal -> Private Link -> Private endpoints -> Create.
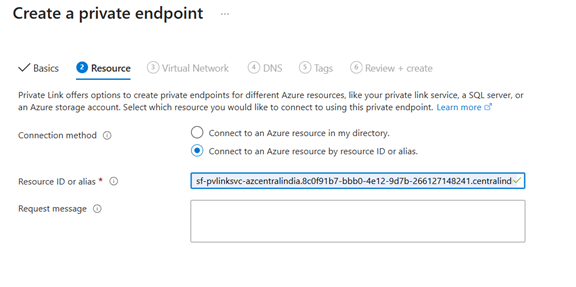
- 17. Basics: Resource group, name (example: pe-snowflake-dla03063), Region: East US 2.
- 18. Resource: choose 'Connect to an Azure resource by resource ID or alias'.
- 20. Paste privatelink-pls-id into 'Resource ID or alias'.
- 21. Networking: select VNet and the Private Endpoint subnet (snet-privatelink-snowflake).
- 22. Review + Create -> Create.
After creation, capture the Private Endpoint private IP from the associated network interface. In this implementation, the Private Endpoint IP is 10.0.0.4 (example).
3.5 Create Private DNS Zone
The DNS zone name must be privatelink.snowflakecomputing.com. Link it to your VNet with auto-registration turned off.
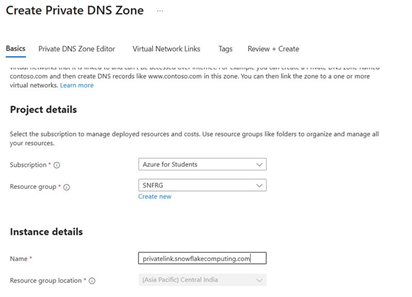
- 23. Azure Portal -> Private DNS zones -> Create.
- 24. Name: privatelink.snowflakecomputing.com
- 25. Place in the same resource group (recommended).
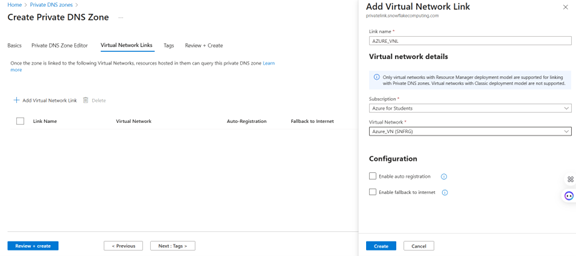
- 27. Open the DNS zone -> Virtual network links -> Add.
- 28. Link to your VNet (where clients run).
- 29. Auto-registration: Off.
- 30. Create.
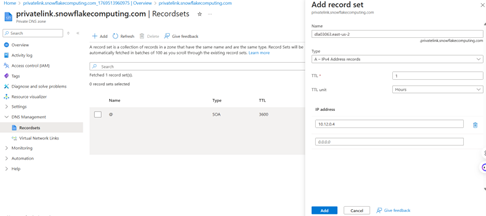
3.6 Create DNS Records
All hostnames returned by SYSTEM$GET_PRIVATELINK_CONFIG() that end with snowflakecomputing.com must resolve to the Private Endpoint IP in your VNet. Create A records in the Private DNS zone privatelink.snowflakecomputing.com pointing to 10.0.0.4 (your Private Endpoint IP).
| Azure record set Name | FQDN | Purpose |
|---|---|---|
| dla03063.east-us-2.privatelink | dla03063.east-us-2.privatelink.snowflakecomputing.com | SQL endpoint (region-specific) |
| tvypihz-yca28219.privatelink | tvypihz-yca28219.privatelink.snowflakecomputing.com | SQL endpoint (regionless) |
| app.east-us-2.privatelink | app.east-us-2.privatelink.snowflakecomputing.com | Snowsight (region-specific) |
| app-tvypihz-yca28219.privatelink | app-tvypihz-yca28219.privatelink.snowflakecomputing.com | Snowsight (regionless) |
| ocsp.dla03063.east-us-2.privatelink | ocsp.dla03063.east-us-2.privatelink.snowflakecomputing.com | OCSP (region-specific) |
| ocsp.tvypihz-yca28219.privatelink | ocsp.tvypihz-yca28219.privatelink.snowflakecomputing.com | OCSP (regionless) |
| tvypihz-yca28219.openflow.iadzpr.privatelink | tvypihz-yca28219.openflow.iadzpr.privatelink.snowflakecomputing.com | Openflow service |
| tvypihz-yca28219.telemetry.iadzpr.privatelink | tvypihz-yca28219.telemetry.iadzpr.privatelink.snowflakecomputing.com | External telemetry |
| tvypihz-yca28219.registry.privatelink | tvypihz-yca28219.telemetry.iadzpr.privatelink.snowflakecomputing.com | SPCS registry |
| sfc-endpoint-login.iadzpr.privatelink | sfc-endpoint-login.iadzpr.privatelink.snowflakecomputing.com | SPCS auth endpoint |
Important DNS rules:
- Do not add 0.0.0.0 as an additional IP in any record set.
- The Azure record set Name must match the left side exactly (it commonly includes '.privatelink').
- Testing from a laptop or Azure Cloud Shell will not resolve this zone unless your device is connected to the VNet (VPN) or you test from a VM inside the VNet.
4. Snowflake Implementation Steps
4.1 Retrieve PrivateLink Configuration
This is the source of truth for all PrivateLink hostnames and the PLS ID required for the Azure Private Endpoint.
USE ROLE ACCOUNTADMIN;
SELECT SYSTEM$GET_PRIVATELINK_CONFIG();4.2 Authorize Azure Private Endpoint
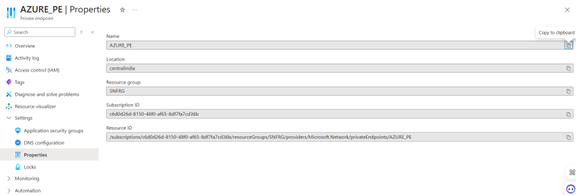
You need the Azure Private Endpoint resource ID and an Azure access token. First, get the resource ID and token from Azure CLI:
-- Get Azure Private Endpoint resource ID:
az network private-endpoint show --name pe-snowflake --resource-group rg-snowflake --query id -o tsv
-- Get Azure access token:
az account get-access-token --subscription <SUBSCRIPTION_ID>Then authorize the endpoint in Snowflake (ACCOUNTADMIN):
USE ROLE ACCOUNTADMIN;
SELECT SYSTEM$AUTHORIZE_PRIVATELINK('<azure-private-endpoint-resource-id>', '<azure-token>');4.3 Verify Authorization
Confirm the endpoint has been authorized successfully:
USE ROLE ACCOUNTADMIN;
SELECT SYSTEM$GET_PRIVATELINK_AUTHORIZED_ENDPOINTS();4.4 Optional - Enforce PrivateLink-Only Access
Warning: Run this only after you have validated DNS + connectivity from within the VNet. Enforcing PrivateLink-only access will block all public internet access to your Snowflake account. If you enforce this too early, you will be locked out from the web UI and any non-VNet clients.
USE ROLE ACCOUNTADMIN;
SELECT SYSTEM$ENFORCE_PRIVATELINK();Rollback if needed:
-- Rollback: re-enable public access
USE ROLE ACCOUNTADMIN;
SELECT SYSTEM$DISABLE_PRIVATELINK();5. Validation and Testing
5.1 Validate DNS Resolution
Important: You must test DNS resolution from inside the VNet (e.g., a VM inside vnet-data-prod or an equivalent workload VNet). Do not test from Azure Cloud Shell or from a laptop on the public internet -- Azure Cloud Shell does not run inside your VNet, so it cannot resolve Private DNS zones.
nslookup dla03063.east-us-2.privatelink.snowflakecomputing.comExpected result: The hostname resolves to the Private Endpoint IP (e.g., 10.0.0.4). If it resolves to a public IP or fails to resolve, check your Private DNS zone configuration and VNet link.
Also verify the Snowsight and OCSP hostnames:
nslookup app.east-us-2.privatelink.snowflakecomputing.com
nslookup ocsp.dla03063.east-us-2.privatelink.snowflakecomputing.comAll hostnames should resolve to the same Private Endpoint private IP (e.g., 10.0.0.4).
5.2 Validate HTTPS and SQL Connectivity
From the VNet VM, test HTTPS connectivity to the SQL endpoint:
curl -v https://dla03063.east-us-2.privatelink.snowflakecomputing.comA successful response (HTTP 200 or TLS handshake success) confirms that the Private Endpoint is routing traffic correctly to Snowflake.
Snowsight (from browser inside the VNet VM):
https://app.east-us-2.privatelink.snowflakecomputing.com
5.3 Client connection strings (when connected via VNet/VPN)
Use these hostnames from SYSTEM$GET_PRIVATELINK_CONFIG():
- SQL: dla03063.east-us-2.privatelink.snowflakecomputing.com
- Snowsight: app.east-us-2.privatelink.snowflakecomputing.com
- Regionless SQL (optional): tvypihz-yca28219.privatelink.snowflakecomputing.com
6. Rollback Steps
If something goes wrong or you need to revert changes, follow these rollback procedures.
6.1 Disable PrivateLink Enforcement
If you enforced PrivateLink-only access too early and are locked out, run this from a VNet-connected client or contact Snowflake Support:
USE ROLE ACCOUNTADMIN;
SELECT SYSTEM$DISABLE_PRIVATELINK();This re-enables public internet access to your Snowflake account.
6.2 Revoke Authorized Endpoints
If you need to revoke an authorized Azure Private Endpoint:
USE ROLE ACCOUNTADMIN;
SELECT SYSTEM$REVOKE_PRIVATELINK('<AZURE_PRIVATE_ENDPOINT_RESOURCE_ID>');After revoking, the Private Endpoint will no longer be able to route traffic to your Snowflake account.
Conclusion
Implementing Azure Private Link with Snowflake ensures that all traffic between your Azure workloads and Snowflake stays on the Microsoft backbone network, never traversing the public internet. This runbook covered the end-to-end process, from creating Azure networking resources (VNet, Subnets, Private Endpoint, Private DNS) to authorizing and validating the connection in Snowflake. With PrivateLink enabled, you can securely share data across cloud providers and implement governance, security, and cost optimization strategies for your Snowflake environment.
Frequently Asked Questions
Q: What Snowflake edition is required for PrivateLink?
Business Critical or higher. Standard and Enterprise editions do not support PrivateLink.
Q: Can I test PrivateLink DNS from Azure Cloud Shell?
No. Azure Cloud Shell does not run inside your VNet, so it cannot resolve Private DNS zones. You must test from a VM inside the linked VNet.
Q: How do I lock down Snowflake to only allow PrivateLink connections?
Run SYSTEM$ENFORCE_PRIVATELINK() as ACCOUNTADMIN. This blocks all public internet access. Only run this after validating connectivity from your VNet.
Q: What happens if I enforce PrivateLink too early?
You will be locked out of Snowflake from the web UI and any non-VNet clients. Use SYSTEM$DISABLE_PRIVATELINK() to roll back.
Q: Can I still access Snowflake over the public internet after enabling Private Link?
Yes. By default, enabling Private Link does not disable public access. Public and private connectivity coexist unless you explicitly enforce PrivateLink-only access using SYSTEM$ENFORCE_PRIVATELINK(). You should only enforce this after fully validating private connectivity.
Q: How do I test if DNS resolution is working correctly for PrivateLink?
You must test DNS resolution from a VM or workload inside the Azure Virtual Network linked to the Private DNS zone. Run nslookup against the PrivateLink hostnames (for example, your account's .privatelink.snowflakecomputing.com URL). If the hostname resolves to the Private Endpoint's private IP address (such as 10.0.0.4), DNS is configured correctly. Testing from Azure Cloud Shell or a laptop on the public internet will not work.
Related Articles
Still have questions?
Get AssistanceReady? Let's Talk!
Get expert insights and answers tailored to your business requirements and transformation.
Get Assistance